Faster, cheaper and more scalable
The advancements in artificial intelligence are reshaping the landscape of cybersecurity, with AI now the single biggest force in the network. AI can discover vulnerabilities faster, it can execute highly scalable automated attacks, and it can help malware adapt and change to avoid detection or gain new capability. In cybersecurity defense, AI is used for real-time threat detection, and it facilitates automated response and triage capabilities, too. But part of the trouble comes from within, where companies are increasingly deploying AI tools without properly securing them, creating entirely new risks for businesses to consider.
The internet is run by machines
Human users versus hackers is no longer a model that applies when it comes to internet security. AI and bot traffic is growing far faster than human user traffic, and automation has given way to AI-driven fraud, account takeovers, credential stuffing and scraping and more. Large-scale attacks are far easier and cheaper to deploy, allowing a literal explosion of bots and automated traffic – machines running machines – across the internet.
You are the product
Free games aren’t really free. Even what seems to be a harmless activity can become a conduit of valuable data, conducting surveillance and recording information. Individual bits of data may not have great meaning, but in aggregate it might. The telemetry gained from devices and applications provides location information, networking and proximity data and more. The exchange of convenience or enjoyment for security and privacy is a well-known tradeoff that bad actors exploit continuously.
Identity is the new attack surface
It used to be that cybersecurity focused on the devices – the endpoints which represented the way into the network. Endpoint security is essential, yet it is the user identity which is the vulnerable element. It has been said that bad actors aren’t hacking systems any longer, they’re just logging in. This means that stolen credentials drive the majority of system breaches. Breaking into and highjacking active sessions, bypassing MFA challenges, and performing other identity-based attacks is now forcing a shift toward continuous authentication and a completely Zero Trust (never trust, always verify) security model.
Cybersecurity has never been easy, but it is harder than ever now that AI is involved. There’s a market out there for enabling the bad guys, like cybercrime as a business model. It’s organized and scalable and terrifying. More than ever before, cyber risk is tied directly to business risk, making security something far more than just IT.
Make Sense?
 J
J



 Make Sense?
Make Sense?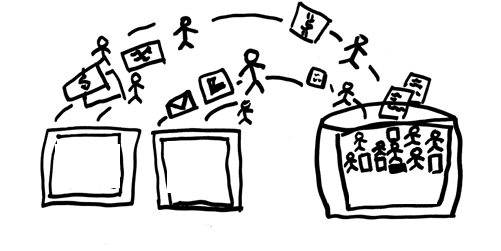 For example, with an installation of QuickBooks accounting the point-of-sale “master location” on the host, the core financial data is able to be secured and protected in the virtual environment without risking lost productivity (and lost sales!) due to connectivity failures at the retail locations. The end-of-day process at each location is to then copy the POS data to the host system where it is integrated with the accounting system. If the POS system is something other than QuickBooks POS, it simply means that there is another piece of software – the specific POS integration tool – required to transfer the POS data into the accounting software. QuickBooks desktop accounting integrations are available for most popular POS systems including Micros, POSiTouch, Aloha and others. The integration software (often just a QuickBooks plug-in) would be installed on the computer running QuickBooks, enabling the entry of the POS data into the QuickBooks accounting system.
For example, with an installation of QuickBooks accounting the point-of-sale “master location” on the host, the core financial data is able to be secured and protected in the virtual environment without risking lost productivity (and lost sales!) due to connectivity failures at the retail locations. The end-of-day process at each location is to then copy the POS data to the host system where it is integrated with the accounting system. If the POS system is something other than QuickBooks POS, it simply means that there is another piece of software – the specific POS integration tool – required to transfer the POS data into the accounting software. QuickBooks desktop accounting integrations are available for most popular POS systems including Micros, POSiTouch, Aloha and others. The integration software (often just a QuickBooks plug-in) would be installed on the computer running QuickBooks, enabling the entry of the POS data into the QuickBooks accounting system. In most regions around the country high-speed broadband is readily available, and using the Internet for working and playing online is a part of everyday life. Facebook and Twitter and Instagram are household names and just about every conversation starts or ends with a reference to a
In most regions around the country high-speed broadband is readily available, and using the Internet for working and playing online is a part of everyday life. Facebook and Twitter and Instagram are household names and just about every conversation starts or ends with a reference to a  Make Sense?
Make Sense?